HashiCorp Vault's New AI Agent Security Features: Questions and Answers
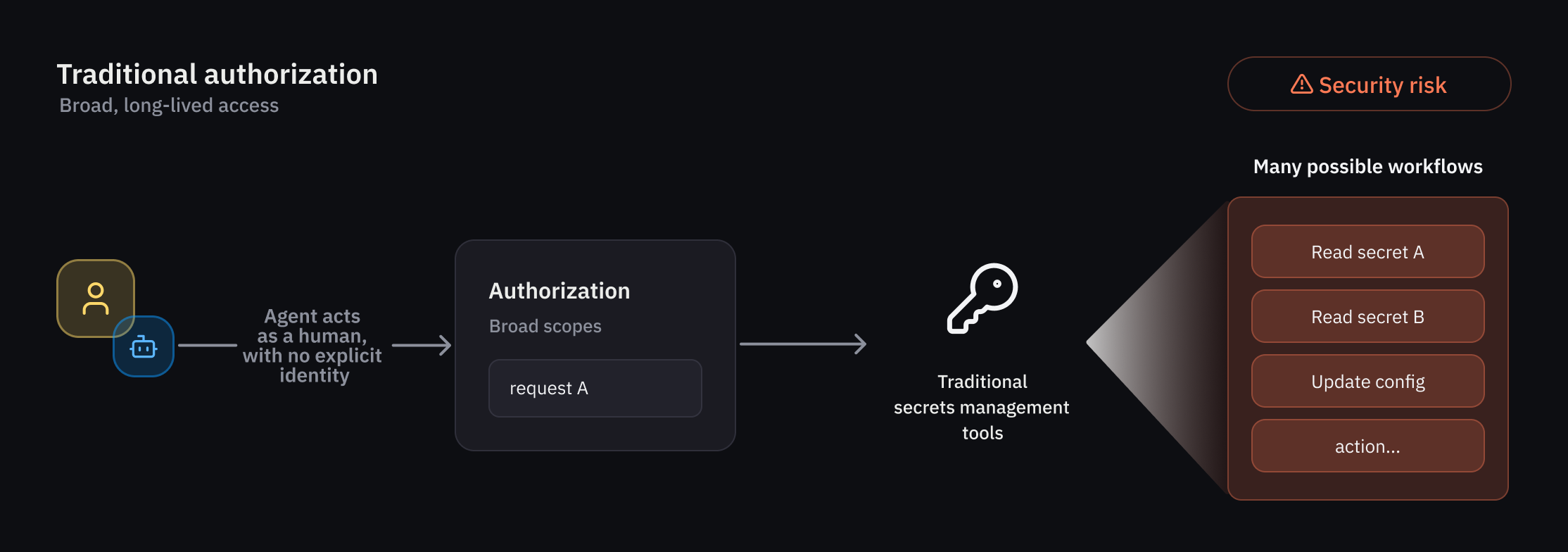
As organizations integrate AI agents into their workflows, traditional identity and access management (IAM) systems—designed for predictable users and processes—fall short. AI agents act autonomously and non-deterministically, requiring dynamic authorization that maps tightly to their identity and is temporary, runtime-evaluated, and scoped to specific transaction contexts. HashiCorp Vault has introduced new capabilities specifically for agentic workflows, including an agent registry, granular identity-based policies, and per-request ephemeral authorization. Below, we answer key questions about these features.
1. Why do AI agents need a fundamentally different authorization model compared to traditional IAM?
Traditional IAM systems are built for deterministic users and workflows—humans and scripts that follow predictable patterns. AI agents, however, are autonomous and non-deterministic; their behavior can change based on real-time data and decisions. This introduces unique security challenges. They require more than static access controls: they need identity-based authorization that is temporary, tightly scoped to the specific request’s context, and evaluated at runtime. Additionally, agents often act on behalf of human users (on-behalf-of pattern), which demands clear delegation tracking. HashiCorp Vault addresses these needs with a new set of controls designed specifically for agentic workloads, ensuring that each agent's actions are attributed and auditable while minimizing risk through ephemeral permissions.
2. What is the agent registry, and how does it differ from managing human or traditional non-human identities?
The agent registry is a new primitive in Vault that allows developers to register and manage AI agent identities separately from human users and traditional non-human identities (NHIs) like service accounts or API keys. This separate oversight is crucial because agents operate with different risk profiles and delegation flows. For example, when an agent uses an on-behalf-of (OBO) pattern, the registry ensures that the delegation from a human user is explicitly tracked and consented. This forms the starting point for a dedicated framework covering registration, authorization, credential management, and observability. By isolating agent identities, administrators can apply policies tailored to their non-deterministic behavior, making it easier to enforce guardrails and audit actions across environments.
3. How does Vault enforce granular, identity-based policies for AI agents?
Least-privilege access is a top priority, and Vault addresses it with a rich set of policy-based runtime controls for agents. Because agent behavior can be non-deterministic, Vault applies deterministic guardrails—such as predefined policies—combined with per-request access control evaluated at runtime. Administrators can define fine-grained policies that scope permissions to individual actions, workflows, or even specific transaction contexts. Since agents often operate in delegation mode (carrying the authority of a human user), Vault evaluates trust across multiple dimensions. For instance, it checks the agent's identity, the delegating user's identity, and the specific request context before granting access to secrets or credentials. This ensures that agents only have the necessary permissions for the immediate task, reducing the risk of abuse.
4. What is ephemeral (per-request) authorization, and why is it important for AI agents?
Ephemeral authorization grants temporary access rights that expire after a specific task or timeframe. This is critical for AI agents because their actions are less predictable than traditional workloads. Instead of giving an agent a long-lived credential, Vault issues a short-lived token or secret that is valid only for the duration of a single request or a defined session. This minimizes the blast radius if an agent is compromised—an attacker cannot reuse stale credentials. It also aligns with the dynamic nature of agentic workflows, where each action may require different resources. By coupling ephemeral authorization with runtime policy evaluation, Vault ensures that every access attempt is independently verified, providing strong security for autonomous systems.
5. How does Vault handle the delegation and consent process when AI agents act on behalf of users?
When an AI agent acts on behalf of a human user (on-behalf-of pattern), Vault enforces a delegation and consent framework. The agent registry explicitly tracks this delegation, ensuring that the human user has consented to the agent performing specific actions. During a request, Vault evaluates the agent's identity, the user's identity, and any consent policies, then applies runtime authorization that takes all three factors into account. This provides clear attribution and auditability—every action can be traced back to both the agent and the delegating user. Administrators can set guardrails to prevent agents from exceeding the scope of delegated authority, and consent can be revoked dynamically. This approach builds trust while enabling autonomous workflows.
6. When will these new AI agent features be publicly available, and how can organizations start using them?
Currently, these capabilities—the agent registry, granular identity-based policies, and ephemeral authorization—are being evaluated by select customers through an early access program. HashiCorp plans to release a broader public beta in a future Vault update this summer. Organizations interested in early access can contact HashiCorp to join the program. Once the public beta launches, users will be able to register agents, define policies, and implement per-request authorization for their agentic workflows. The general availability timeline will follow based on feedback and testing during the beta phase. These features are designed to provide a standardized, secure approach to managing AI agent identities across diverse environments.